what are the two rrs that network utopia needs to register to its tld domain?
The Domain Proper name Arrangement (DNS) is the hierarchical and decentralized naming arrangement used to identify computers, services, and other resources reachable through the Internet or other Internet Protocol (IP) networks. The resources records contained in the DNS acquaintance domain names with other forms of information. These are about normally used to map human-friendly domain names to the numerical IP addresses computers need to locate services and devices using the underlying network protocols, merely have been extended over time to perform many other functions also. The Domain Name System has been an essential component of the functionality of the Internet since 1985.
Part
An often-used illustration to explain the Domain Proper name Organization is that it serves as the phone book for the Internet by translating human-friendly computer hostnames into IP addresses. For example, the domain proper noun world wide web.example.com translates to the addresses 93.184.216.34 (IPv4) and 2606:2800:220:1:248:1893:25c8:1946 (IPv6). The DNS tin can be quickly and transparently updated, allowing a service's location on the network to change without affecting the end users, who keep to use the same hostname. Users take advantage of this when they use meaningful Compatible Resource Locators (URLs) and electronic mail addresses without having to know how the estimator actually locates the services.
An important and ubiquitous function of the DNS is its fundamental role in distributed Net services such as cloud services and content delivery networks.[1] When a user accesses a distributed Cyberspace service using a URL, the domain name of the URL is translated to the IP accost of a server that is proximal to the user. The fundamental functionality of the DNS exploited here is that unlike users tin simultaneously receive different translations for the same domain proper name, a cardinal point of divergence from a traditional phone-book view of the DNS. This procedure of using the DNS to assign proximal servers to users is key to providing faster and more reliable responses on the Cyberspace and is widely used by most major Internet services.[2]
The DNS reflects the construction of authoritative responsibleness in the Cyberspace.[3] Each subdomain is a zone of administrative autonomy delegated to a director. For zones operated by a registry, administrative information is ofttimes complemented past the registry's RDAP and WHOIS services. That data tin can be used to gain insight on, and track responsibility for, a given host on the Internet.[iv]
History
Using a simpler, more memorable name in place of a host's numerical address dates back to the ARPANET era. The Stanford Research Institute (at present SRI International) maintained a text file named HOSTS.TXT that mapped host names to the numerical addresses of computers on the ARPANET.[v] [6] Elizabeth Feinler developed and maintained the first ARPANET directory.[7] [viii] Maintenance of numerical addresses, called the Assigned Numbers List, was handled by Jon Postel at the University of Southern California'southward Information Sciences Constitute (ISI), whose team worked closely with SRI.[9]
Addresses were assigned manually. Computers, including their hostnames and addresses, were added to the primary file by contacting the SRI Network Information Heart (NIC), directed by Feinler, telephone during business hours.[10] Later on, Feinler set up a WHOIS directory on a server in the NIC for retrieval of data about resources, contacts, and entities.[xi] She and her team adult the concept of domains.[11] Feinler suggested that domains should be based on the location of the physical address of the reckoner.[12] Computers at educational institutions would have the domain edu, for instance.[13] She and her team managed the Host Naming Registry from 1972 to 1989.[xiv]
By the early 1980s, maintaining a single, centralized host table had go slow and unwieldy and the emerging network required an automated naming organisation to address technical and personnel bug. Postel directed the task of forging a compromise betwixt five competing proposals of solutions to Paul Mockapetris. Mockapetris instead created the Domain Proper noun System in 1983 while at the University of Southern California.[10] [xv]
The Internet Engineering Task Force published the original specifications in RFC 882 and RFC 883 in Nov 1983.[16] [17]
In 1984, four UC Berkeley students, Douglas Terry, Mark Painter, David Riggle, and Songnian Zhou, wrote the beginning Unix name server implementation for the Berkeley Internet Name Domain, commonly referred to every bit Bind.[18] In 1985, Kevin Dunlap of DEC essentially revised the DNS implementation. Mike Karels, Phil Almquist, and Paul Vixie and then took over BIND maintenance. Internet Systems Consortium was founded in 1994 past Rick Adams, Paul Vixie, and Carl Malamud, expressly to provide a abode for Bind development and maintenance. Bind versions from 4.9.3 onward were developed and maintained past ISC, with support provided by ISC'due south sponsors. As co-architects/programmers, Bob Halley and Paul Vixie released the showtime production-ready version of BIND version 8 in May 1997. Since 2000, over 43 different core developers have worked on BIND. [nineteen]
In Nov 1987, RFC 1034[xx] and RFC 1035[three] superseded the 1983 DNS specifications. Several additional Request for Comments take proposed extensions to the core DNS protocols.[21]
Structure
Domain proper name space
The domain name space consists of a tree information structure. Each node or foliage in the tree has a label and zero or more than resource records (RR), which hold data associated with the domain proper name. The domain name itself consists of the label, concatenated with the name of its parent node on the right, separated by a dot.[22]
The tree sub-divides into zones commencement at the root zone. A DNS zone may consist of just i domain, or may consist of many domains and sub-domains, depending on the authoritative choices of the zone manager. DNS tin can also exist partitioned according to class where the separate classes can exist idea of equally an array of parallel namespace trees.[23]
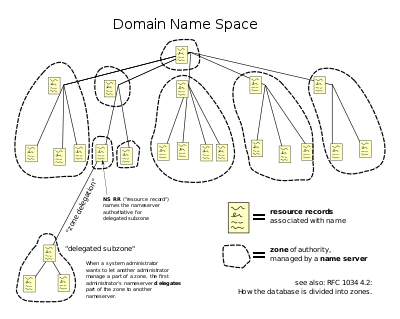
The hierarchical Domain Name Organization for grade Net, organized into zones, each served by a name server
Administrative responsibility for any zone may be divided by creating boosted zones. Authorisation over the new zone is said to exist delegated to a designated name server. The parent zone ceases to be authoritative for the new zone.[23]
Domain name syntax, internationalization
The definitive descriptions of the rules for forming domain names appear in RFC 1035, RFC 1123, RFC 2181, and RFC 5892. A domain name consists of one or more parts, technically called labels, that are conventionally concatenated, and delimited by dots, such every bit example.com.
The right-most label conveys the meridian-level domain; for example, the domain name www.example.com belongs to the height-level domain com.
The hierarchy of domains descends from correct to left; each label to the left specifies a subdivision, or subdomain of the domain to the correct. For example, the label case specifies a subdomain of the com domain, and www is a subdomain of example.com. This tree of subdivisions may have up to 127 levels.[24]
A characterization may comprise zero to 63 characters. The null label, of length null, is reserved for the root zone. The full domain name may non exceed the length of 253 characters in its textual representation.[xx] In the internal binary representation of the DNS the maximum length requires 255 octets of storage, as it also stores the length of the name.[3]
Although no technical limitation exists to prevent domain proper noun labels using any character which is representable by an octet, hostnames use a preferred format and grapheme gear up. The characters immune in labels are a subset of the ASCII grapheme set up, consisting of characters a through z, A through Z, digits 0 through 9, and hyphen. This rule is known as the LDH dominion (letters, digits, hyphen). Domain names are interpreted in case-independent manner.[25] Labels may not start or end with a hyphen.[26] An additional rule requires that tiptop-level domain names should not be all-numeric.[26]
The limited gear up of ASCII characters permitted in the DNS prevented the representation of names and words of many languages in their native alphabets or scripts. To make this possible, ICANN approved the Internationalizing Domain Names in Applications (IDNA) organization, by which user applications, such every bit spider web browsers, map Unicode strings into the valid DNS character ready using Punycode. In 2009 ICANN approved the installation of internationalized domain proper noun land code top-level domains (ccTLDs). In addition, many registries of the existing top-level domain names (TLDsouthward) take adopted the IDNA system, guided by RFC 5890, RFC 5891, RFC 5892, RFC 5893.
Proper noun servers
The Domain Proper name Organization is maintained by a distributed database organization, which uses the client–server model. The nodes of this database are the name servers. Each domain has at least i administrative DNS server that publishes information about that domain and the proper noun servers of any domains subordinate to it. The peak of the hierarchy is served by the root name servers, the servers to query when looking upward (resolving) a TLD.
An administrative name server is a name server that but gives answers to DNS queries from data that has been configured by an original source, for case, the domain administrator or by dynamic DNS methods, in contrast to answers obtained via a query to some other name server that only maintains a cache of data.
An authoritative name server tin can either be a primary server or a secondary server. Historically the terms chief/slave and main/secondary were sometimes used interchangeably[27] but the current practice is to use the latter form. A main server is a server that stores the original copies of all zone records. A secondary server uses a special automatic updating machinery in the DNS protocol in advice with its primary to maintain an identical re-create of the master records.
Every DNS zone must be assigned a set of administrative name servers. This set of servers is stored in the parent domain zone with name server (NS) records.
An authoritative server indicates its status of supplying definitive answers, deemed authoritative, past setting a protocol flag, called the "Authoritative Answer" (AA) bit in its responses.[iii] This flag is usually reproduced prominently in the output of DNS administration query tools, such as dig, to indicate that the responding name server is an authority for the domain name in question. [3]
When a proper noun server is designated as the administrative server for a domain proper noun for which it does non have authoritative data, it presents a type of error chosen a "lame delegation" or "lame response".[28] [29]
Operation
Address resolution machinery
Domain name resolvers decide the domain proper name servers responsible for the domain name in question by a sequence of queries starting with the right-most (top-level) domain label.

A DNS resolver that implements the iterative approach mandated by RFC 1034; in this case, the resolver consults three name servers to resolve the fully qualified domain name "www.wikipedia.org".
For proper operation of its domain name resolver, a network host is configured with an initial cache (hints) of the known addresses of the root name servers. The hints are updated periodically past an administrator by retrieving a dataset from a reliable source.
Assuming the resolver has no cached records to accelerate the process, the resolution process starts with a query to 1 of the root servers. In typical functioning, the root servers do not answer directly, but respond with a referral to more than authoritative servers, due east.k., a query for "world wide web.wikipedia.org" is referred to the org servers. The resolver now queries the servers referred to, and iteratively repeats this process until it receives an authoritative answer. The diagram illustrates this process for the host that is named past the fully qualified domain name "world wide web.wikipedia.org".
This mechanism would place a large traffic burden on the root servers, if every resolution on the Internet required starting at the root. In practice caching is used in DNS servers to off-load the root servers, and every bit a result, root proper noun servers really are involved in only a relatively small fraction of all requests.
Recursive and caching name server
In theory, authoritative name servers are sufficient for the operation of the Internet. However, with but authoritative name servers operating, every DNS query must starting time with recursive queries at the root zone of the Domain Name System and each user organization would have to implement resolver software capable of recursive functioning.[30]
To meliorate efficiency, reduce DNS traffic across the Net, and increase operation in end-user applications, the Domain Name Organization supports DNS cache servers which store DNS query results for a period of time determined in the configuration (time-to-alive) of the domain name tape in question. Typically, such caching DNS servers also implement the recursive algorithm necessary to resolve a given name starting with the DNS root through to the authoritative proper noun servers of the queried domain. With this office implemented in the name server, user applications gain efficiency in blueprint and functioning.
The combination of DNS caching and recursive functions in a name server is not mandatory; the functions tin be implemented independently in servers for special purposes.
Internet service providers typically provide recursive and caching name servers for their customers. In addition, many abode networking routers implement DNS caches and recursion to improve efficiency in the local network.
DNS resolvers
The client side of the DNS is called a DNS resolver. A resolver is responsible for initiating and sequencing the queries that ultimately pb to a full resolution (translation) of the resource sought, e.g., translation of a domain proper noun into an IP address. DNS resolvers are classified past a variety of query methods, such equally recursive, non-recursive, and iterative. A resolution process may apply a combination of these methods.[20]
In a non-recursive query, a DNS resolver queries a DNS server that provides a record either for which the server is authoritative, or information technology provides a fractional consequence without querying other servers. In example of a caching DNS resolver, the not-recursive query of its local DNS cache delivers a issue and reduces the load on upstream DNS servers by caching DNS resource records for a period of time later an initial response from upstream DNS servers.
In a recursive query, a DNS resolver queries a single DNS server, which may in turn query other DNS servers on behalf of the requester. For example, a simple stub resolver running on a home router typically makes a recursive query to the DNS server run by the user'southward Isp. A recursive query is one for which the DNS server answers the query completely past querying other name servers as needed. In typical performance, a client problems a recursive query to a caching recursive DNS server, which subsequently issues non-recursive queries to determine the answer and send a single answer dorsum to the client. The resolver, or some other DNS server acting recursively on behalf of the resolver, negotiates use of recursive service using bits in the query headers. DNS servers are not required to support recursive queries.
The iterative query process is a process in which a DNS resolver queries a chain of 1 or more than DNS servers. Each server refers the client to the next server in the chain, until the current server can fully resolve the request. For case, a possible resolution of www.case.com would query a global root server, and so a "com" server, and finally an "example.com" server.
Round dependencies and glue records
Name servers in delegations are identified by name, rather than by IP accost. This means that a resolving proper name server must issue another DNS request to observe out the IP address of the server to which information technology has been referred. If the name given in the delegation is a subdomain of the domain for which the delegation is being provided, there is a round dependency.
In this instance, the name server providing the delegation must besides provide one or more IP addresses for the authoritative name server mentioned in the delegation. This information is called gum. The delegating name server provides this glue in the form of records in the additional section of the DNS response, and provides the delegation in the authorisation department of the response. A mucilage tape is a combination of the proper noun server and IP address.
For instance, if the authoritative name server for example.org is ns1.example.org, a computer trying to resolve www.example.org start resolves ns1.instance.org. As ns1 is independent in instance.org, this requires resolving example.org first, which presents a round dependency. To break the dependency, the name server for the tiptop level domain org includes glue along with the delegation for example.org. The gum records are accost records that provide IP addresses for ns1.case.org. The resolver uses one or more of these IP addresses to query ane of the domain'south authoritative servers, which allows it to consummate the DNS query.
Record caching
A standard practice in implementing name resolution in applications is to reduce the load on the Domain Name Arrangement servers by caching results locally, or in intermediate resolver hosts. Results obtained from a DNS request are always associated with the time to live (TTL), an expiration time after which the results must be discarded or refreshed. The TTL is set by the administrator of the authoritative DNS server. The period of validity may vary from a few seconds to days or even weeks.
Every bit a result of this distributed caching architecture, changes to DNS records do not propagate throughout the network immediately, only require all caches to expire and to exist refreshed later the TTL. RFC 1912 conveys basic rules for determining appropriate TTL values.
Some resolvers may override TTL values, as the protocol supports caching for up to sixty-eight years or no caching at all. Negative caching, i.e. the caching of the fact of non-existence of a record, is determined past proper noun servers authoritative for a zone which must include the Start of Authority (SOA) record when reporting no information of the requested type exists. The value of the minimum field of the SOA tape and the TTL of the SOA itself is used to found the TTL for the negative answer.
Reverse lookup
A opposite DNS lookup is a query of the DNS for domain names when the IP address is known. Multiple domain names may be associated with an IP address. The DNS stores IP addresses in the form of domain names as specially formatted names in pointer (PTR) records inside the infrastructure top-level domain arpa. For IPv4, the domain is in-addr.arpa. For IPv6, the opposite lookup domain is ip6.arpa. The IP address is represented equally a proper noun in contrary-ordered octet representation for IPv4, and opposite-ordered crumb representation for IPv6.
When performing a reverse lookup, the DNS client converts the address into these formats before querying the name for a PTR tape post-obit the delegation chain as for any DNS query. For instance, assuming the IPv4 address 208.eighty.152.two is assigned to Wikimedia, information technology is represented as a DNS name in reverse guild: 2.152.80.208.in-addr.arpa. When the DNS resolver gets a pointer (PTR) request, it begins past querying the root servers, which point to the servers of American Registry for Cyberspace Numbers (ARIN) for the 208.in-addr.arpa zone. ARIN's servers delegate 152.fourscore.208.in-addr.arpa to Wikimedia to which the resolver sends another query for two.152.80.208.in-addr.arpa, which results in an authoritative response.
Client lookup

Users generally do not communicate straight with a DNS resolver. Instead DNS resolution takes place transparently in applications such as web browsers, e-postal service clients, and other Internet applications. When an application makes a request that requires a domain name lookup, such programs transport a resolution asking to the DNS resolver in the local operating system, which in plough handles the communications required.
The DNS resolver will almost invariably take a enshroud (see above) containing contempo lookups. If the enshroud tin provide the answer to the request, the resolver volition return the value in the cache to the plan that fabricated the asking. If the cache does not contain the respond, the resolver will transport the request to one or more designated DNS servers. In the instance of most habitation users, the Internet service provider to which the machine connects will ordinarily supply this DNS server: such a user volition either have configured that server'due south address manually or allowed DHCP to set information technology; all the same, where systems administrators have configured systems to use their own DNS servers, their DNS resolvers point to separately maintained name servers of the organisation. In any event, the name server thus queried volition follow the process outlined to a higher place, until it either successfully finds a result or does not. It and so returns its results to the DNS resolver; bold it has found a result, the resolver duly caches that result for time to come use, and easily the result dorsum to the software which initiated the request.
Broken resolvers
Some large ISPs accept configured their DNS servers to violate rules, such as past disobeying TTLs, or past indicating that a domain name does not exist simply because one of its name servers does not reply.[31]
Some applications such as web browsers maintain an internal DNS cache to avert repeated lookups via the network. This practice can add extra difficulty when debugging DNS issues as information technology obscures the history of such data. These caches typically use very brusque caching times on the guild of ane minute.[32]
Net Explorer represents a notable exception: versions upwards to IE 3.ten cache DNS records for 24 hours by default. Cyberspace Explorer 4.x and later versions (upward to IE 8) decrease the default timeout value to half an hour, which may be inverse past modifying the default configuration.[33]
When Google Chrome detects issues with the DNS server information technology displays a specific error message.
Other applications
The Domain Name System includes several other functions and features.
Hostnames and IP addresses are not required to match in a 1-to-ane relationship. Multiple hostnames may correspond to a single IP address, which is useful in virtual hosting, in which many web sites are served from a single host. Alternatively, a unmarried hostname may resolve to many IP addresses to facilitate fault tolerance and load distribution to multiple server instances beyond an enterprise or the global Internet.
DNS serves other purposes in addition to translating names to IP addresses. For example, mail transfer agents use DNS to detect the best mail server to deliver electronic mail: An MX record provides a mapping between a domain and a mail exchanger; this can provide an additional layer of fault tolerance and load distribution.
The DNS is used for efficient storage and distribution of IP addresses of blacklisted email hosts. A common method is to identify the IP address of the subject host into the sub-domain of a higher level domain name, and to resolve that proper name to a tape that indicates a positive or a negative indication.
For example:
- The address 102.3.iv.5 is blacklisted. It points to 5.4.3.102.blacklist.example, which resolves to 127.0.0.1.
- The accost 102.3.4.6 is not blacklisted and points to half dozen.4.iii.102.blacklist.example. This hostname is either not configured, or resolves to 127.0.0.2.
E-mail servers can query blacklist.case to find out if a specific host connecting to them is in the blacklist. Many of such blacklists, either subscription-based or complimentary of price, are available for apply by email administrators and anti-spam software.
To provide resilience in the event of computer or network failure, multiple DNS servers are unremarkably provided for coverage of each domain. At the pinnacle level of global DNS, thirteen groups of root name servers be, with boosted "copies" of them distributed worldwide via anycast addressing.
Dynamic DNS (DDNS) updates a DNS server with a client IP address on-the-wing, for example, when moving betwixt ISPs or mobile hot spots, or when the IP address changes administratively.
DNS bulletin format
The DNS protocol uses two types of DNS letters, queries and replies; both have the same format. Each message consists of a header and 4 sections: question, answer, authority, and an additional space. A header field (flags) controls the content of these 4 sections.[twenty]
The header section consists of the following fields: Identification, Flags, Number of questions, Number of answers, Number of authorisation resource records (RRs), and Number of additional RRs. Each field is 16 bits long, and appears in the order given. The identification field is used to match responses with queries. The flag field consists of sub-fields as follows:
| Field | Description | Length (bits) |
|---|---|---|
| QR | Indicates if the message is a query (0) or a respond (1) | 1 |
| OPCODE | The type can be QUERY (standard query, 0), IQUERY (inverse query, 1), or STATUS (server status request, two) | iv |
| AA | Authoritative Reply, in a response, indicates if the DNS server is authoritative for the queried hostname | ane |
| TC | TrunCation, indicates that this message was truncated due to excessive length | 1 |
| RD | Recursion Desired, indicates if the client means a recursive query | 1 |
| RA | Recursion Bachelor, in a response, indicates if the replying DNS server supports recursion | 1 |
| Z | Zippo, reserved for future use | 3 |
| RCODE | Response lawmaking, can be NOERROR (0), FORMERR (1, Format error), SERVFAIL (2), NXDOMAIN (iii, Nonexistent domain), etc.[34] | 4 |
After the flag, the header ends with four xvi-bit integers which contain the number of records in each of the sections that follow, in the same order.
Question section
The question department has a simpler format than the resource record format used in the other sections. Each question record (at that place is commonly merely one in the section) contains the following fields:
| Field | Clarification | Length (octets) |
|---|---|---|
| NAME | Name of the requested resource | Variable |
| Type | Blazon of RR (A, AAAA, MX, TXT, etc.) | 2 |
| Course | Class code | 2 |
The domain name is broken into detached labels which are concatenated; each label is prefixed past the length of that characterization.[35]
DNS ship protocols
DNS-over-UDP/53 ("Do53")
From the time of its origin in 1983 until quite recently, DNS has primarily answered queries on User Datagram Protocol (UDP) port number 53.[iii] Such queries consist of a clear-text request sent in a single UDP parcel from the client, responded to with a clear-text respond sent in a single UDP packet from the server. When the length of the reply exceeds 512 bytes and both client and server back up Extension Mechanisms for DNS (EDNS), larger UDP packets may be used.[36] Use of DNS-over-UDP is express by, among other things, its lack of transport-layer encryption, authentication, reliable delivery, and message length.
DNS-over-TCP/53 ("Do53/TCP")
In 1989, RFC 1123 specified optional Transmission Command Protocol (TCP) transport for DNS queries, replies and, particularly, zone transfers. Via fragmentation of long replies, TCP allows longer responses, reliable delivery, and re-apply of long-lived connections between clients and servers.
DNSCrypt
The DNSCrypt protocol, which was developed in 2011 exterior the IETF standards framework, introduced DNS encryption on the downstream side of recursive resolvers, wherein clients encrypt query payloads using servers' public keys, which are published in the DNS (rather than relying upon third-party document authorities) and which may in turn exist protected by DNSSEC signatures.[37] DNSCrypt uses either TCP or UDP port 443, the same port every bit HTTPS encrypted web traffic. This introduced not only privacy regarding the content of the query, simply besides a significant measure of firewall-traversal adequacy. In 2019, DNSCrypt was farther extended to support an "anonymized" style, like to the proposed "Oblivious DNS," in which an ingress node receives a query which has been encrypted with the public key of a different server, and relays it to that server, which acts as an egress node, performing the recursive resolution.[38] Privacy of user/query pairs is created, since the ingress node does not know the content of the query, while the egress nodes does not know the identity of the customer. DNSCrypt was first implemented in production by OpenDNS in December of 2011.
DNS-over-TLS ("DoT")
An IETF standard for encrypted DNS emerged in 2016, utilizing standard Transport Layer Security (TLS) to protect the entire connexion, rather than just the DNS payload. DoT servers listen on TCP port 853. RFC7858 specifies that opportunistic encryption and authenticated encryption may exist supported, but did non brand either server or client authentication mandatory.
DNS-over-HTTPS ("DoH")
A competing standard for DNS query transport was introduced in 2018, tunneling DNS query information over HTTPS (which in plow transports HTTP over TLS). DoH was promoted as a more than web-friendly alternative to DNS since, similar DNSCrypt, it travels on TCP port 443, and thus looks similar to web traffic, though they are easily differentiable in exercise.[39] DoH has been widely criticized for decreasing user anonymity relative to DoT.[40]
DNS-over-TOR
Like other Internet protocols, DNS may be run over VPNs and tunnels. Ane utilise which has get common enough since 2019 to warrant its ain frequently used acronym is DNS-over-Tor. The privacy gains of Oblivious DNS can be garnered through the utilize of the preexisting Tor network of ingress and egress nodes, paired with the transport-layer encryption provided by TLS.[41]
Oblivious DNS-over-HTTPS ("ODoH")
In 2021, an "oblivious" implementation of DoH was proposed and has been implemented in draft form, combining ingress/egress separation with HTTPS tunneling and TLS transport-layer encryption in a single defined protocol.[42]
Resource records
The Domain Name System specifies a database of information elements for network resources. The types of data elements are categorized and organized with a list of DNS record types, the resources records (RRs). Each tape has a type (name and number), an expiration time (time to live), a grade, and type-specific data. Resources records of the same type are described as a resources tape set (RRset), having no special ordering. DNS resolvers return the entire gear up upon query, only servers may implement round-robin ordering to reach load balancing. In contrast, the Domain Name System Security Extensions (DNSSEC) work on the consummate prepare of resource tape in approved order.
When sent over an Internet Protocol network, all records use the common format specified in RFC 1035:[43]
| Field | Description | Length (octets) |
|---|---|---|
| Proper noun | Name of the node to which this tape pertains | Variable |
| Type | Type of RR in numeric course (e.yard., 15 for MX RRs) | ii |
| CLASS | Class code | two |
| TTL | Count of seconds that the RR stays valid (The maximum is 231−ane, which is near 68 years) | 4 |
| RDLENGTH | Length of RDATA field (specified in octets) | 2 |
| RDATA | Additional RR-specific information | Variable, as per RDLENGTH |
Proper name is the fully qualified domain name of the node in the tree[ clarification needed ]. On the wire, the name may exist shortened using label compression where ends of domain names mentioned earlier in the bundle can be substituted for the end of the current domain name.
Blazon is the tape type. It indicates the format of the information and it gives a hint of its intended utilise. For instance, the A tape is used to translate from a domain proper noun to an IPv4 address, the NS record lists which proper name servers can reply lookups on a DNS zone, and the MX record specifies the mail server used to handle mail for a domain specified in an e-mail accost.
RDATA is data of type-specific relevance, such every bit the IP address for accost records, or the priority and hostname for MX records. Well known record types may use label compression in the RDATA field, but "unknown" tape types must non (RFC 3597).
The CLASS of a record is set to IN (for Internet) for common DNS records involving Internet hostnames, servers, or IP addresses. In improver, the classes Chaos (CH) and Hesiod (HS) exist.[44] Each class is an independent proper name space with potentially different delegations of DNS zones.
In addition to resource records divers in a zone file, the domain name system too defines several request types that are used only in advice with other DNS nodes (on the wire), such equally when performing zone transfers (AXFR/IXFR) or for EDNS (OPT).
Wildcard DNS records
The domain proper name system supports wildcard DNS records which specify names that start with the asterisk characterization, '*', e.k., *.example.[20] [45] DNS records belonging to wildcard domain names specify rules for generating resource records within a single DNS zone by substituting whole labels with matching components of the query proper noun, including whatsoever specified descendants. For instance, in the following configuration, the DNS zone ten.instance specifies that all subdomains, including subdomains of subdomains, of ten.example utilize the mail exchanger (MX) a.10.instance. The A record for a.10.case is needed to specify the mail exchanger IP address. As this has the result of excluding this domain proper noun and its subdomains from the wildcard matches, an additional MX tape for the subdomain a.ten.example, as well equally a wildcarded MX record for all of its subdomains, must besides exist defined in the DNS zone.
ten.example. MX 10 a.x.instance. *.x.case. MX 10 a.x.example. *.a.ten.example. MX ten a.x.example. a.x.instance. MX 10 a.x.case. a.x.example. AAAA 2001:db8::1 The role of wildcard records was refined in RFC 4592, because the original definition in RFC 1034 was incomplete and resulted in misinterpretations by implementers.[45]
Protocol extensions
The original DNS protocol had limited provisions for extension with new features. In 1999, Paul Vixie published in RFC 2671 (superseded past RFC 6891) an extension mechanism, chosen Extension Mechanisms for DNS (EDNS) that introduced optional protocol elements without increasing overhead when not in employ. This was accomplished through the OPT pseudo-resource record that merely exists in wire transmissions of the protocol, but not in whatever zone files. Initial extensions were also suggested (EDNS0), such as increasing the DNS bulletin size in UDP datagrams.
Dynamic zone updates
Dynamic DNS updates use the UPDATE DNS opcode to add or remove resource records dynamically from a zone database maintained on an authoritative DNS server. The feature is described in RFC 2136. This facility is useful to register network clients into the DNS when they boot or become otherwise available on the network. As a booting client may exist assigned a different IP address each fourth dimension from a DHCP server, it is not possible to provide static DNS assignments for such clients.
Security problems
Originally, security concerns were not major blueprint considerations for DNS software or any software for deployment on the early Net, as the network was not open for participation by the general public. Even so, the expansion of the Internet into the commercial sector in the 1990s changed the requirements for security measures to protect data integrity and user authentication.
Several vulnerability issues were discovered and exploited by malicious users. One such result is DNS cache poisoning, in which information is distributed to caching resolvers under the pretense of being an authoritative origin server, thereby polluting the data store with potentially false data and long expiration times (time-to-live). Subsequently, legitimate awarding requests may be redirected to network hosts operated with malicious intent.
DNS responses traditionally do not have a cryptographic signature, leading to many attack possibilities; the Domain Name Organization Security Extensions (DNSSEC) change DNS to add support for cryptographically signed responses. DNSCurve has been proposed as an alternative to DNSSEC. Other extensions, such equally TSIG, add together support for cryptographic authentication between trusted peers and are commonly used to authorize zone transfer or dynamic update operations.
Some domain names may be used to accomplish spoofing furnishings. For example, paypal.com and paypa1.com are dissimilar names, even so users may be unable to distinguish them in a graphical user interface depending on the user's called typeface. In many fonts the letter l and the numeral 1 await very like or fifty-fifty identical. This problem is astute in systems that back up internationalized domain names, as many character codes in ISO 10646 may announced identical on typical figurer screens. This vulnerability is occasionally exploited in phishing.[46]
Techniques such as forward-confirmed opposite DNS can also be used to aid validate DNS results.
DNS tin can also "leak" from otherwise secure or private connections, if attending is not paid to their configuration, and at times DNS has been used to bypass firewalls past malicious persons, and exfiltrate data, since it is often seen as innocuous.
Privacy and tracking problems
Originally designed equally a public, hierarchical, distributed and heavily cached database, DNS protocol has no confidentiality controls. User queries and nameserver responses are being sent unencrypted which enables network packet sniffing, DNS hijacking, DNS cache poisoning and homo-in-the-middle attacks. This deficiency is commonly used by cybercriminals and network operators for marketing purposes, user authentication on captive portals and censorship.[47]
User privacy is further exposed by proposals for increasing the level of client IP information in DNS queries (RFC 7871) for the do good of Content Delivery Networks.
The main approaches that are in apply to counter privacy issues with DNS:
- VPNs, which move DNS resolution to the VPN operator and hibernate user traffic from local Internet access provider,
- Tor, which replaces traditional DNS resolution with anonymous .onion domains, hiding both proper noun resolution and user traffic behind onion routing counter-surveillance,
- Proxies and public DNS servers, which move the bodily DNS resolution to a third-party provider, who ordinarily promises lilliputian or no request logging and optional added features, such as DNS-level advertisement or pornography blocking.
- Public DNS servers can be queried using traditional DNS protocol, in which instance they provide no protection from local surveillance, or DNS-over-HTTPS, DNS-over-TLS and DNSCrypt, which practice provide such protection
Solutions preventing DNS inspection by local network operator are criticized for thwarting corporate network security policies and Internet censorship. They are as well criticized from a privacy point of view, every bit giving away the DNS resolution to the hands of a modest number of companies known for monetizing user traffic and for centralizing DNS name resolution, which is generally perceived as harmful for the Internet.[47]
Google is the dominant provider of the platform in Android, the browser in Chrome, and the DNS resolver in the viii.8.viii.8 service. Would this scenario exist a case of a single corporate entity beingness in a position of overarching command of the unabridged namespace of the Internet? Netflix already fielded an app that used its own DNS resolution machinery independent of the platform upon which the app was running. What if the Facebook app included DoH? What if Apple's iOS used a DoH-resolution mechanism to bypass local DNS resolution and steer all DNS queries from Apple tree's platforms to a ready of Apple-operated name resolvers?
—DNS Privacy and the IETF
Domain name registration
The right to use a domain name is delegated by domain name registrars which are accredited by the Internet Corporation for Assigned Names and Numbers (ICANN) or other organizations such as OpenNIC, that are charged with overseeing the name and number systems of the Internet. In addition to ICANN, each top-level domain (TLD) is maintained and serviced technically past an administrative system, operating a registry. A registry is responsible for operating the database of names within its authoritative zone, although the term is about oft used for TLDs. A registrant is a person or organization who asked for domain registration.[21] The registry receives registration information from each domain proper name registrar, which is authorized (accredited) to assign names in the corresponding zone and publishes the data using the WHOIS protocol. As of 2015, usage of RDAP is existence considered.[48]
ICANN publishes the consummate list of TLDs, TLD registries, and domain name registrars. Registrant information associated with domain names is maintained in an online database attainable with the WHOIS service. For most of the more than 290 country code acme-level domains (ccTLDs), the domain registries maintain the WHOIS (Registrant, name servers, expiration dates, etc.) data. For instance, DENIC, Germany NIC, holds the DE domain data. From almost 2001, most Generic acme-level domain (gTLD) registries accept adopted this and so-chosen thick registry approach, i.e. keeping the WHOIS data in key registries instead of registrar databases.
For elevation-level domains on COM and Internet, a thin registry model is used. The domain registry (e.g., GoDaddy, BigRock and PDR, VeriSign, etc., etc.) holds basic WHOIS data (i.e., registrar and name servers, etc.). Organizations, or registrants using ORG on the other manus, are on the Public Interest Registry exclusively.
Some domain proper noun registries, often chosen network data centers (NIC), also function as registrars to end-users, in addition to providing access to the WHOIS datasets. The top-level domain registries, such as for the domains COM, NET, and ORG use a registry-registrar model consisting of many domain name registrars.[49] In this method of management, the registry merely manages the domain proper noun database and the human relationship with the registrars. The registrants (users of a domain proper name) are customers of the registrar, in some cases through additional subcontracting of resellers.
RFC documents
Standards
The Domain Proper name System is divers by Request for Comments (RFC) documents published by the Internet Technology Task Force (Internet standards). The following is a list of RFCs that define the DNS protocol.
- RFC 1034, Domain Names - Concepts and Facilities
- RFC 1035, Domain Names - Implementation and Specification
- RFC 1123, Requirements for Internet Hosts—Application and Back up
- RFC 1995, Incremental Zone Transfer in DNS
- RFC 1996, A Machinery for Prompt Notification of Zone Changes (DNS NOTIFY)
- RFC 2136, Dynamic Updates in the domain name organization (DNS UPDATE)
- RFC 2181, Clarifications to the DNS Specification
- RFC 2308, Negative Caching of DNS Queries (DNS NCACHE)
- RFC 2672, Not-Terminal DNS Name Redirection
- RFC 2845, Secret Primal Transaction Hallmark for DNS (TSIG)
- RFC 3225, Indicating Resolver Support of DNSSEC
- RFC 3226, DNSSEC and IPv6 A6 aware server/resolver bulletin size requirements
- RFC 3596, DNS Extensions to Support IP Version six
- RFC 3597, Handling of Unknown DNS Resource Record (RR) Types
- RFC 4343, Domain Name System (DNS) Case Insensitivity Clarification
- RFC 4592, The Role of Wildcards in the Domain Name System
- RFC 4635, HMAC SHA TSIG Algorithm Identifiers
- RFC 5001, DNS Proper name Server Identifier (NSID) Option
- RFC 5011, Automated Updates of DNS Security (DNSSEC) Trust Anchors
- RFC 5452, Measures for Making DNS More than Resilient against Forged Answers
- RFC 5890, Internationalized Domain Names for Applications (IDNA):Definitions and Document Framework
- RFC 5891, Internationalized Domain Names in Applications (IDNA): Protocol
- RFC 5892, The Unicode Code Points and Internationalized Domain Names for Applications (IDNA)
- RFC 5893, Right-to-Left Scripts for Internationalized Domain Names for Applications (IDNA)
- RFC 6891, Extension Mechanisms for DNS (EDNS0)
- RFC 7766, DNS Transport over TCP - Implementation Requirements
Proposed security standards
- RFC 4033, DNS Security Introduction and Requirements
- RFC 4034, Resource Records for the DNS Security Extensions
- RFC 4035, Protocol Modifications for the DNS Security Extensions
- RFC 4509, Use of SHA-256 in DNSSEC Delegation Signer (DS) Resource Records
- RFC 4470, Minimally Covering NSEC Records and DNSSEC On-line Signing
- RFC 5155, DNS Security (DNSSEC) Hashed Authenticated Denial of Existence
- RFC 5702, Use of SHA-two Algorithms with RSA in DNSKEY and RRSIG Resources Records for DNSSEC
- RFC 5910, Domain Name Arrangement (DNS) Security Extensions Mapping for the Extensible Provisioning Protocol (EPP)
- RFC 5933, Utilise of GOST Signature Algorithms in DNSKEY and RRSIG Resource Records for DNSSEC
- RFC 7830, The EDNS(0) Padding Pick
- RFC 7858, Specification for DNS over Transport Layer Security (TLS)
- RFC 8310, Usage Profiles for DNS over TLS and DNS over DTLS
- RFC 8484, DNS Queries over HTTPS (DoH)
Experimental RFCs
- RFC 1183, New DNS RR Definitions
Best Electric current Practices
- RFC 2182, Option and Operation of Secondary DNS Servers (BCP sixteen)
- RFC 2317, Classless IN-ADDR.ARPA delegation (BCP twenty)
- RFC 5625, DNS Proxy Implementation Guidelines (BCP 152)
- RFC 6895, Domain Name Arrangement (DNS) IANA Considerations (BCP 42)
- RFC 7720, DNS Root Name Service Protocol and Deployment Requirements (BCP forty)
Informational RFCs
These RFCs are advisory in nature, but may provide useful information despite defining neither a standard or BCP. (RFC 1796)
- RFC 1178, Choosing a Proper noun for Your Computer (FYI 5)
- RFC 1591, Domain Name System Construction and Delegation
- RFC 1912, Mutual DNS Operational and Configuration Errors
- RFC 2100, The Naming of Hosts
- RFC 3696, Application Techniques for Checking and Transformation of Names
- RFC 3833. Threat Analysis of the Domain Name Arrangement (DNS)
- RFC 4892, Requirements for a Mechanism Identifying a Name Server Example
- RFC 5894, Internationalized Domain Names for Applications (IDNA):Groundwork, Explanation, and Rationale
- RFC 5895, Mapping Characters for Internationalized Domain Names in Applications (IDNA) 2008
- RFC 7626, DNS Privacy Considerations
- RFC 7706, Decreasing Access Fourth dimension to Root Servers by Running 1 on Loopback
- RFC 8499, DNS Terminology
Unknown
These RFCs have an official condition of Unknown, but due to their age are not clearly labeled as such.
- RFC 920, Domain Requirements – Specified original top-level domains
- RFC 1032, Domain Administrators Guide
- RFC 1033, Domain Administrators Operations Guide
- RFC 1101, DNS Encodings of Network Names and Other Types
See as well
- Alternative DNS root
- Comparison of DNS server software
- Domain hijacking
- DNS hijacking
- DNS management software
- DNS over HTTPS
- DNS over TLS
- Hierarchical namespace
- IPv6 brokenness and DNS whitelisting
- Multicast DNS
- Public recursive proper noun server
- resolv.conf
- Split-horizon DNS
- List of DNS record types
- List of managed DNS providers
- Zone file
- DNS leak
References
- ^ J. Dilley, B. Maggs, J. Parikh, H. Prokop, R. Sitaraman, and B. Weihl. "Globally Distributed Content Delivery, IEEE Internet Calculating, September/October 2002, pp. 50-58" (PDF).
- ^ Nygren., Due east.; Sitaraman R. K.; Lord's day, J. (2010). "The Akamai Network: A Platform for High-Performance Internet Applications" (PDF). ACM SIGOPS Operating Systems Review. 44 (3): 2–19. doi:ten.1145/1842733.1842736. S2CID 207181702. Retrieved November 19, 2012.
- ^ a b c d e f Mockapetris, Paul (November 1987). Domain Names - Implementation and Specification. IETF. doi:10.17487/RFC1035. RFC 1035.
- ^ Champika Wijayatunga (February 2015). "DNS Abuse Handling" (PDF). APNIC. Retrieved eighteen December 2016.
- ^ RFC 3467, "Function of the Domain Name System (DNS)", J.C. Klensin, J. Klensin (February 2003).
- ^ Liu, Cricket; Albitz, Paul (2006). DNS and BIND (5th ed.). O'Reilly Media. p. 3. ISBN978-0-596-10057-5.
- ^ Evans 2018, p. 112.
- ^ Evans 2018, p. 113.
- ^ IEEE Register [3B2-ix] man2011030074.3d 29/7/011 eleven:54 Folio 74
- ^ a b "Why Does the Net Still Work on Christmas? Paul Mockapetris - Net Hall of Fame". internethalloffame.org.
- ^ a b Evans 2018, p. 119.
- ^ Evans 2018, p. 120.
- ^ Evans 2018, p. 120–121.
- ^ "Elizabeth Feinler". Cyberspace Hall of Fame. Archived from the original on fourteen September 2018. Retrieved 2018-11-25 .
- ^ "Paul Mockapetris | Internet Hall of Fame". internethalloffame.org . Retrieved 2020-02-12 .
- ^ Andrei Robachevsky (26 Nov 2013). "Happy 30th Birthday, DNS!". Cyberspace Order. Retrieved xviii December 2015.
- ^ Elizabeth Feinler, IEEE Register, 3B2-9 man2011030074.3d 29/vii/011 eleven:54 Page 74
- ^ Terry, Douglas B.; et al. (June 12–15, 1984). "The Berkeley Internet Proper name Domain Server". Summer Conference, Salt Lake Metropolis 1984: Proceedings. USENIX Association Software Tools Users Group. pp. 23–31.
- ^ Internet Systems Consortium. "The History of BIND". History of Bind. Retrieved 4 April 2022.
{{cite spider web}}: CS1 maint: url-status (link) - ^ a b c d e Mockapetris, Paul (Nov 1987). Domain Names - Domain Concepts and Facilities. IETF. doi:10.17487/RFC1034. RFC 1034.
- ^ a b Paul Hoffman; Andrew Sullivan; Kazunori Fujiwara (December 2015). DNS Terminology. IETF. doi:10.17487/RFC7719. RFC 7719. Retrieved 18 December 2015.
- ^ Paul Mockapetris (November 1987). "Name space specifications and terminology". Domain Names - Domain Concepts and Facilities. IETF. sec. 3.i. doi:ten.17487/RFC1034. RFC 1034. Retrieved 17 December 2015.
- ^ a b Paul Mockapetris (November 1987). "How the database is divided into zones". Domain Names - Domain Concepts and Facilities. IETF. sec. 4.2. doi:x.17487/RFC1034. RFC 1034. Retrieved 17 December 2015.
- ^ Lindsay, David (2007). International Domain Name Law: ICANN and the UDRP. Bloomsbury Publishing. p. viii. ISBN978-1-84113-584-vii.
- ^ Network Working Group of the IETF, Jan 2006, RFC 4343: Domain Proper name Organization (DNS) Case Insensitivity Description
- ^ a b RFC 3696, Application Techniques for Checking and Transformation of Names, J. Klensin
- ^ Fujiwara, Kazunori; Sullivan, Andrew; Hoffman, Paul. "DNS Terminology". tools.ietf.org . Retrieved 2020-06-21 .
- ^ Nemeth, Evi; Snyder, Garth; Hein, Trent R. (2006-10-thirty). Linux Administration Handbook. Addison-Wesley Professional. ISBN978-0-13-700275-7.
- ^ Bissyande, Tegawendé F.; Sie, Oumarou (2017-10-09). eastward-Infrastructure and eastward-Services for Developing Countries: 8th International Briefing, AFRICOMM 2016, Ouagadougou, Burkina Faso, December vi-7, 2016, Proceedings. Springer. ISBN978-iii-319-66742-three.
- ^ "DNS zone". IONOS Digitalguide . Retrieved 2022-03-31 .
- ^ "Providers ignoring DNS TTL?". Slashdot. 2005. Retrieved 2012-04-07 .
- ^ Ben Anderson (vii September 2011). "Ben Anderson: Why Web Browser DNS Caching Tin Be A Bad Thing". Retrieved twenty October 2014.
- ^ "How Net Explorer uses the cache for DNS host entries". Microsoft Corporation. 2004. Retrieved 2010-07-25 .
- ^ "Domain Proper name System (DNS) Parameters". IANA. DNS RCODEs. Retrieved 14 June 2019.
- ^ James F. Kurose and Keith W. Ross, Computer Networking: A Peak-Down Approach, sixth ed. Essex, England: Pearson Educ. Express, 2012
- ^ RFC 2671, Extension Mechanisms for DNS (EDNS0), P. Vixie (August 1999)
- ^ Ulevitch, David (6 Dec 2011). "DNSCrypt – Disquisitional, fundamental, and about time". Cisco Umbrella. Archived from the original on 1 July 2020.
- ^ "Anonymized DNSCrypt specification". GitHub. DNSCrypt. Archived from the original on 25 October 2019.
- ^ Csikor, Levente; Divakaran, Dinil Mon (February 2021). "Privacy of DNS-over-HTTPS: Requiem for a Dream?" (PDF). National University of Singapore.
We investigate whether DoH traffic is distinguishable from encrypted Spider web traffic. To this end, we railroad train a automobile learning model to classify HTTPS traffic equally either Web or DoH. With our DoH identification model in place, we show that an authoritarian Internet service provider can identify ~97.4% of the DoH packets correctly while only misclassifying 1 in 10,000 Web packets.
- ^ Posch, Maya (21 October 2019). "DNS-over-HTTPS is the Wrong Fractional Solution". Hackaday.
DoH removes options for network operators (individual and corporate) to secure their own network, as 1 of the architects behind DNS, Paul Vixie, pointed out on Twitter last year. DoH is substantially DNS-over-HTTP-over-TLS, resulting in its own mime Media Blazon of application/dns-message and significant added complication. By mixing DoH in with existing protocols, information technology ways that every DNS request and response goes through an HTTPS stack. For embedded applications this is a nightmare scenario, merely it is also incompatible with near every slice of existing security hardware. When rogue apps like Firefox circumvent the system's DoT-based DNS and utilize its own DNS resolver over DoH instead, this makes for a highly opaque security situation. That DNS resolving would motility into individual applications, as nosotros run into happening now, seems similar a massive step backwards.
- ^ Muffett, Alec (Feb 2021). ""No Port 53, Who Dis?" A Year of DNS over HTTPS over Tor" (PDF). Network and Distributed Organization Security Symposium.
DNS-over-HTTPS (DoH) obviates many but not all of the risks, and its transport protocol (i.e. HTTPS) raises concerns of privacy due to (e.chiliad.) 'cookies.' The Tor Network exists to provide TCP circuits with some freedom from tracking, surveillance, and blocking. Thus: In combination with Tor, DoH, and the principle of "Don't Do That, And so" (DDTT) to mitigate request fingerprinting, I draw DNS over HTTPS over Tor (DoHoT).
- ^ Pauly, Tommy (2 September 2021). "Oblivious DNS Over HTTPS". IETF.
- ^ RFC 5395, Domain Name System (DNS) IANA Considerations, D. Eastlake 3rd (November 2008), Section 3
- ^ RFC 5395, Domain Name Organization (DNS) IANA Considerations, D. Eastlake 3rd (November 2008), p. 11
- ^ a b RFC 4592, The Function of Wildcards in the Domain Name System, E. Lewis (July 2006)
- ^ APWG. "Global Phishing Survey: Domain Name Employ and Trends in 1H2010." ten/15/2010 apwg.org Archived 2012-10-03 at the Wayback Machine
- ^ a b Huston, Geoff (July 2019). "DNS Privacy and the IETF" (PDF). The Internet Protocol Periodical.
- ^ "Registration Data Access Protocol (RDAP) Operational Contour for gTLD Registries and Registrars". ICANN. three Dec 2015. Archived from the original on 22 December 2015. Retrieved 18 Dec 2015.
- ^ "Find a Registrar". VeriSign, Inc. Retrieved 18 December 2015.
Sources
- Evans, Claire L. (2018). Wide Band: The Untold Story of the Women Who Made the Internet. New York: Portfolio/Penguin. ISBN9780735211759.
External links
- Vixie, Paul (2007-04-01). "DNS Complexity". ACM Queue. Archived from the original on 2007-06-10.
- Zytrax.com, Open up Source Guide – DNS for Rocket Scientists.
- Internet Governance and the Domain Name System: Issues for Congress Congressional Research Service
- Ball, James (28 February 2014). "Meet the seven people who hold the keys to worldwide internet security". The Guardian. Guardian News & Media Limited. Retrieved 28 February 2014.
Source: https://en.wikipedia.org/wiki/Domain_Name_System
0 Response to "what are the two rrs that network utopia needs to register to its tld domain?"
Enregistrer un commentaire